Kategorie: Kurse & Leistungen
Erste Hilfe Kurs für Führerschein / BG
Erste Hilfe Kurs für Führerschein / BG Als zugelassene Ausbildungsstelle: […]
Zum Kursangebot
Evakuierungshelfer
Der Arbeitgeber ist verpflichtet, für die Aufgaben im Rahmen der […]
Mehr erfahren
Erste Hilfe Ausbilder Lehrgang pädagogischer Teil 24 UE
Erste Hilfe Ausbilder Lehrgang pädagogischer Teil 24 UE Erste Hilfe […]
Zum Kursangebot
Erste Hilfe Ausbilder Fortbildung 16 UE (E-Learning 8 UE / Präsens 8 UE) 2023
Erste Hilfe Ausbilder Fortbildung 16 UE (E-Learning 8 UE / […]
Zum Kursangebot
Erste Hilfe Ausbilder Lehrgang Fachdidaktik Teil 32 UE / Lehrprobe
Erste Hilfe Ausbilder Lehrgang Fachdidaktik Teil 32 UE / Lehrprobe […]
Zum Kursangebot
American Heart Association ACLS Provider Kurs
American Heart Association ACLS Provider Kurs Kursbeschreibung: Der AHA ACLS […]
Zum Kursangebot
American Heart Association BLS Provider Kurs
American Heart Association BLS Provider Kurs Basisreanimation für medizinisches Fachpersonal […]
Zum Kursangebot
Lehrprogrammbezogenen Einweisung für Betriebssanitäter Ausbilder
Lehrprogrammbezogenen Einweisung für Betriebssanitäter Ausbilder – gem. Berufsgenossenschaft (BG) Ausbilder […]
Zum Kursangebot
Jährliche Unterweisung §12 Arbeitsschutzgesetz
Jährliche Unterweisung §12 Arbeitsschutzgesetz Weitere Informationen
Zum Kursangebot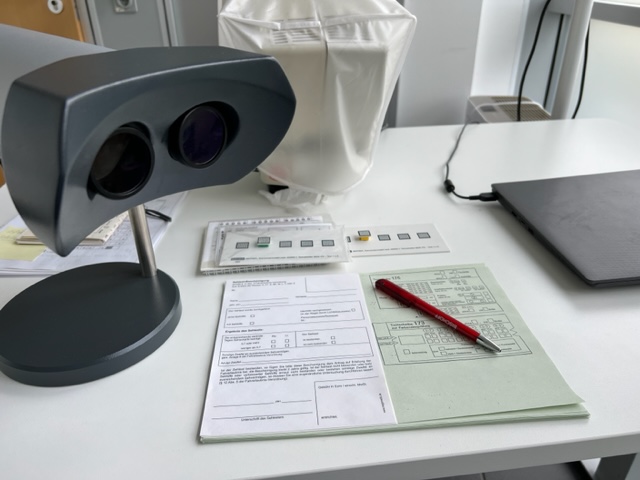
Sehtester Lehrgang (E-Learning)
Sehtester Lehrgang (E-Learning) Dieser Kurs wird in Form eines Zoom-Meeting […]
Zum Kursangebot
American Heart Association PALS Instructoren Kurs
American Heart Association PALS Instructoren Kurs In einer AHA-Kursleiterschulung werden […]
Zum Kursangebot
American Heart Association PALS Provider Kurs
American Heart Association PALS Provider Kurs Jetzt mit PALS Provider […]
Zum Kursangebot
American Heart Association PEARS Provider Kurs
American Heart Association PEARS Kurs Jetzt mit PALS Provider Buch […]
Zum Kursangebot
American Heart Association ACLS Instructoren Kurs
American Heart Association ACLS Instructoren Kurs In einer AHA-Kursleiterschulung werden […]
Zum Kursangebot
American Heart Association BLS Instruktoren Kurs
American Heart Association BLS Instruktoren Kurs In einer AHA-Kursleiterschulung werden […]
Zum Kursangebot
Notfalltraining
Ein Notfalltraining für Senioren- und Pflegeeinrichtungen vor Ort Weitere Informationen
Zum Kursangebot
Betriebssanitäter Ausbilder Fortbildung - gem. Berufsgenossenschaft (BG)
Betriebssanitäter Ausbilder Fortbildung – gem. Berufsgenossenschaft (BG) Ausbilder bzw. Ausbilderin […]
Zum Kursangebot
Lehrprogrammbezogenen Einweisung für Erste Hilfe Ausbilder Kinder und Betreuungseinrichtungen
Lehrprogrammbezogenen Einweisung für Erste Hilfe Ausbilder Kinder und Betreuungseinrichtungen gem. […]
Zum Kursangebot
Betriebssanitäter Grundkurs
Betriebssanitäter Grundkurs Grundsätzliches Notwendig ist ein Betriebssanitäter generell, wenn in […]
Zum Kursangebot
Betriebssanitäter Aufbaukurs
Betriebssanitäter Aufbaukurs Die Teilnehmer machen sich auf der Grundlage der […]
Zum Kursangebot
Betriebssanitäter Fortbildung
Betriebssanitäter Fortbildung Die Lernpartner werden auf der Grundlage der im […]
Zum KursangebotEH-Ausbildung für Personal in Bildungs- und Betreuungseinrichtungen
EH-Ausbildung für Personal in Bildungs- und Betreuungseinrichtungen Für Erzieher, Lehrer […]
Zum Kursangebot
Erste Hilfe Kurs für gehörlose nach den BG Vorgaben / FeV §68
Erste Hilfe Kurs für gehörlose nach den BG Vorgaben / […]
Zum KursangebotEH-Ausbildung für gehörlose für Personal in Bildungs- und Betreuungseinrichtungen
EH-Ausbildung für gehörlose für Personal in Bildungs- und Betreuungseinrichtungen Für […]
Zum Kursangebot